For financial entities, risk leaders, and compliance teams
Digital Operational
Resilience Act
(DORA) Compliance
Operationalize DORA across ICT risk management, major incident reporting, resilience testing, and third-party oversight with one accountable workflow.
What is the Digital Operational Resilience Act (DORA)?
DORA (Regulation (EU) 2022/2554) is the EU's regulation ensuring that financial entities can withstand, respond to, and recover from ICT-related disruptions. It became fully applicable on 17 January 2025 and covers over 20 categories of financial entities, from banks and insurers to crypto-asset service providers.
DORA also establishes an EU oversight framework for designated critical ICT third-party providers and acts as lex specialis to NIS2 for financial-sector ICT risk and incident reporting obligations.
Timeline and Compliance Milestones
DORA became fully applicable on 17 January 2025 after a two-year preparation period. Technical standards and CTPP designations are now in place, with ongoing oversight and testing obligations. Use this timeline to sequence readiness work against supervisory expectations.
European Commission proposes DORA as part of the Digital Finance Package
Regulation published in the Official Journal; 24-month preparation period begins
DORA becomes fully applicable. Compliance is now mandatory for all financial entities
ESAs designate first 19 Critical Third-Party Providers including AWS, Google Cloud, and Microsoft
Annual Register of Information reporting enters a recurring cycle under ESA implementing standards and national authority timelines
Commission review deadline for key DORA provisions, including oversight and reporting framework effectiveness (Article 60)
European Commission proposes DORA as part of the Digital Finance Package
Regulation published in the Official Journal; 24-month preparation period begins
DORA becomes fully applicable. Compliance is now mandatory for all financial entities
ESAs designate first 19 Critical Third-Party Providers including AWS, Google Cloud, and Microsoft
Annual Register of Information reporting enters a recurring cycle under ESA implementing standards and national authority timelines
Commission review deadline for key DORA provisions, including oversight and reporting framework effectiveness (Article 60)
European Commission proposes DORA as part of the Digital Finance Package
Regulation published in the Official Journal; 24-month preparation period begins
DORA becomes fully applicable. Compliance is now mandatory for all financial entities
ESAs designate first 19 Critical Third-Party Providers including AWS, Google Cloud, and Microsoft
Annual Register of Information reporting enters a recurring cycle under ESA implementing standards and national authority timelines
Commission review deadline for key DORA provisions, including oversight and reporting framework effectiveness (Article 60)
Who is Subject to DORA?
DORA covers 20+ types of financial entities under Article 2(1), from banks and insurers to crypto providers. It also reaches into the technology supply chain through its oversight framework for designated critical ICT third-party providers.
Banking & Credit
- Credit institutions
- Payment institutions
- Electronic money institutions
- Account information service providers
Investment & Trading
- Investment firms
- Trading venues
- Central securities depositories
- Central counterparties
Insurance & Pensions
- Insurance and reinsurance undertakings
- Insurance intermediaries
- Institutions for occupational retirement provision
Crypto & Alternative
- Crypto-asset service providers
- Crowdfunding service providers
- Securitisation repositories
Asset Management
- Management companies
- Alternative investment fund managers
Market Infrastructure
- Trade repositories
- Credit rating agencies
- Administrators of critical benchmarks
- Data reporting service providers
Proportionality Principle (Article 4)
DORA applies proportionally: requirements scale with the size, risk profile, and complexity of the entity.
Article 16(1) provides a simplified ICT risk management framework for certain entity categories, including relevant microenterprises and selected lower-risk institutions.
Other in-scope institutions must implement the full framework, and entities identified by competent authorities must perform advanced resilience testing (TLPT) under Articles 26-27.
DORA Reaches Into Your Tech Supply Chain
DORA's Chapter V brings ICT third-party service providers into scope through oversight of Critical Third-Party Providers (CTPPs). On 18 November 2025, the European Supervisory Authorities designated the first 19 CTPPs, including AWS, Google Cloud, and Microsoft.
Extraterritorial reach (Article 31(12)): Non-EU CTPPs must establish a subsidiary within the European Union within 12 months of designation. This means a US cloud provider serving EU financial institutions cannot simply comply from abroad; they must have an EU legal presence.
Contractual obligations (Article 28): Even non-critical ICT providers are affected. Financial entities must include specific contractual clauses covering audit rights, data location, incident notification, and exit strategies in all ICT service agreements.
The 5 Pillars of DORA
DORA is structured around five compliance pillars that together ensure digital operational resilience across the financial sector.
ICT Risk Management
- -Comprehensive ICT risk management framework
- -Management body accountability and oversight
- -Identify, protect, detect, respond, and recover
- -Business continuity and disaster recovery plans
Incident Reporting
- -Classify incidents based on severity criteria
- -Initial notification within 4 hours of classification (and within 24 hours of awareness)
- -Intermediate report within 72 hours of the initial notification
- -Final report within 1 month of the latest updated intermediate report
Resilience Testing
- -Regular testing of ICT tools and systems
- -Threat-Led Penetration Testing (TLPT) at least every 3 years for designated entities
- -External testers required for at least every third TLPT
- -Testing on live production systems with safeguards
- -Follow DORA TLPT RTS for execution and closure requirements
Third-Party Risk
- -Register of Information for all ICT contracts
- -Due diligence before onboarding providers
- -Continuous monitoring of provider performance
- -Direct oversight of critical ICT providers by ESAs
Information Sharing
- -Voluntary cyber threat intelligence sharing
- -Within trusted financial sector communities
- -Compliant with data protection rules
- -Collective defense across the sector
Incident Reporting Timeline
DORA incident reporting RTS sets a strict three-stage timeline for major ICT-related incidents.
Initial Notification
Report within 4 hours of classifying a major ICT incident and no later than 24 hours after becoming aware of it.
Intermediate Report
Submit an updated assessment within 72 hours from the initial notification.
Final Report
Deliver the final report within one month of the latest updated intermediate report.
Penalties for Non-Compliance
DORA sets the enforcement framework, but sanctions for most financial entities are defined by Member State law rather than a single EU-wide fine table.
Financial Entities
Member States must provide effective, proportionate, and dissuasive penalties for breaches by in-scope financial entities.
Critical ICT Providers
Lead overseers can impose periodic penalty payments on designated critical ICT third-party providers under Article 35.
Periodic Penalty Window
The periodic penalty payment for designated critical ICT providers can run daily for up to six months.
How Modulos Helps with DORA Compliance
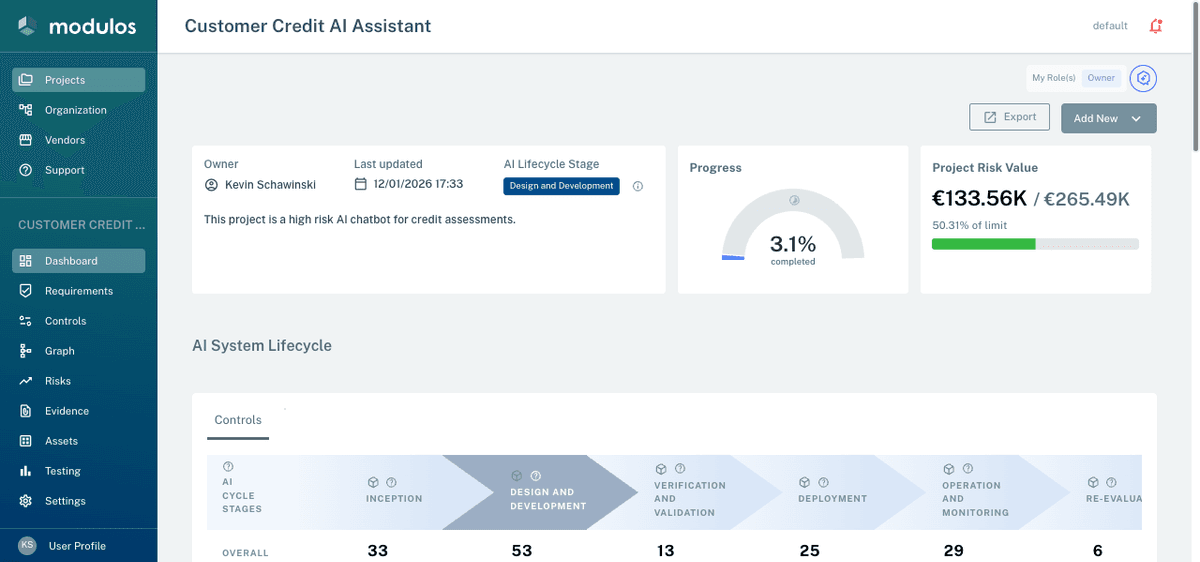
Modulos gives risk and compliance teams one workflow for requirements, controls, evidence, reviews, and exports. This helps you operationalize DORA with clearer accountability and defensible audit trails.
Book a DORA DemoBreak DORA obligations into structured requirements and mapped controls with clear ownership, implementation status, and evidence expectations.
FAQ about DORA
DORA (Digital Operational Resilience Act, Regulation EU 2022/2554) is the EU's regulation ensuring financial entities can withstand, respond to, and recover from ICT-related disruptions. It became fully applicable on 17 January 2025.
DORA applies to over 20 types of financial entities, including banks, payment institutions, investment firms, insurers, crypto-asset service providers, and market infrastructures. It also creates an EU oversight regime for ICT third-party providers that are designated as critical.
The five pillars are: (1) ICT Risk Management, covering comprehensive frameworks for identifying and managing ICT risks; (2) Incident Reporting, covering classification and reporting of major ICT incidents; (3) Digital Operational Resilience Testing, including regular testing and threat-led penetration testing; (4) ICT Third-Party Risk Management, covering risks from ICT service providers; (5) Information Sharing, enabling voluntary cyber threat intelligence sharing.
For financial entities, DORA requires Member States to set effective, proportionate, and dissuasive penalties in national law, so sanctions are not harmonized into one EU-wide fine cap. For designated critical ICT third-party providers, lead overseers can impose periodic penalty payments of up to 1% of average daily worldwide turnover per day for up to six months (Article 35).
DORA is lex specialis (sector-specific law) to NIS2's lex generalis (general law). For financial entities subject to both, DORA takes precedence on ICT risk management, incident reporting, and resilience testing. NIS2's broader governance and supply chain requirements may still apply where DORA does not specifically cover.
Under the DORA incident reporting RTS, financial entities submit an initial notification within 4 hours after classifying a major ICT incident (and no later than 24 hours after becoming aware of it), an intermediate report within 72 hours of the initial notification, and a final report within one month of the latest updated intermediate report.
TLPT is an advanced resilience testing requirement for designated financial entities. DORA requires TLPT at least every three years, generally on live production systems with safeguards, and requires use of external testers for at least every third TLPT. Detailed execution rules are set in the DORA TLPT RTS.
Modulos helps teams operationalize DORA with structured requirements, control mapping, linked evidence, review workflows, and exportable audit documentation. This supports traceable governance execution and clearer supervisory-readiness across the DORA pillars.
Need a Defensible DORA Execution Workflow?
In a live walkthrough, see how teams track ICT risk controls, third-party evidence, and reporting artifacts before supervisory reviews.